How OTP verification works and why it matters
How OTP verification works and why it matters is a cornerstone of modern online security. This guide breaks down the process, the delivery methods, and how to implement best practices to protect user accounts. For practical use, you can explore an OTP service page on SMSPVA here or read our detailed post on OTP verification on the SMSPVA blog, including real-world tips and precautions. You can also learn from external resources like WhatsApp for alternative delivery channels, Google Safety, and Wikipedia: One-time password.
Why use OTP verification
OTP verification provides an extra layer beyond static passwords. Its benefits include:
- Improved account security by requiring possession of a code sent to a trusted channel
- Reduced risk of credential stuffing and SIM-swapping when paired with server-side protections
- Flexibility to deliver codes via SMS, voice calls, or app-based generators
- Better user trust when services show clear consent and privacy safeguards
How to implement OTP verification
- Choose a delivery method (SMS, voice, or app-based token) based on your audience and risks
- Generate a short, unique code with proper entropy and an expiration window (e.g., 5 minutes)
- Validate the code on your server with rate limiting and retry protection
- Verify the user’s session only after successful code validation
- Protect the code from exposure (do not log full codes, use short-lived storage)
- Provide fallback options and clear error messaging if delivery fails
- Comply with local privacy laws and obtain user consent for sending codes
For a concrete example, a common flow uses SMS OTP, but you may also consider app-based OTP for higher security. When integrating, you can reference our OTP services page https://smspva.com/service/otp for implementation ideas. If you’re curious about how these codes travel, see Wikipedia: One-time password and Google Safety.
Comparison and troubleshooting
| Aspect | SMS OTP | Voice OTP | App-based OTP |
|---|---|---|---|
| Delivery speed | Nearly instant | Instant after call | Fast but depends on device |
| Cost | Low to moderate | Moderate | Usually higher due to app infrastructure |
| Reliability | High in good coverage areas | Depends on call quality | Very reliable if device is accessible |
| Security considerations | Phone number exposure risk | Voice interception risk | Strong if using TOTP or push |
| User experience | Simple, familiar | Requires answering call | Best UX with push/app |
Safe and legal use
Always obtain user consent, inform about data handling, and store only what is necessary. Follow local regulations for sending codes, retain logs according to policy, and provide opt-out options where required. For security best practices, review guidelines from Google Safety and official service docs.
FAQ
- What is OTP verification?
- An OTP verification uses a short, time-limited code sent to the user to confirm identity during login or sensitive actions.
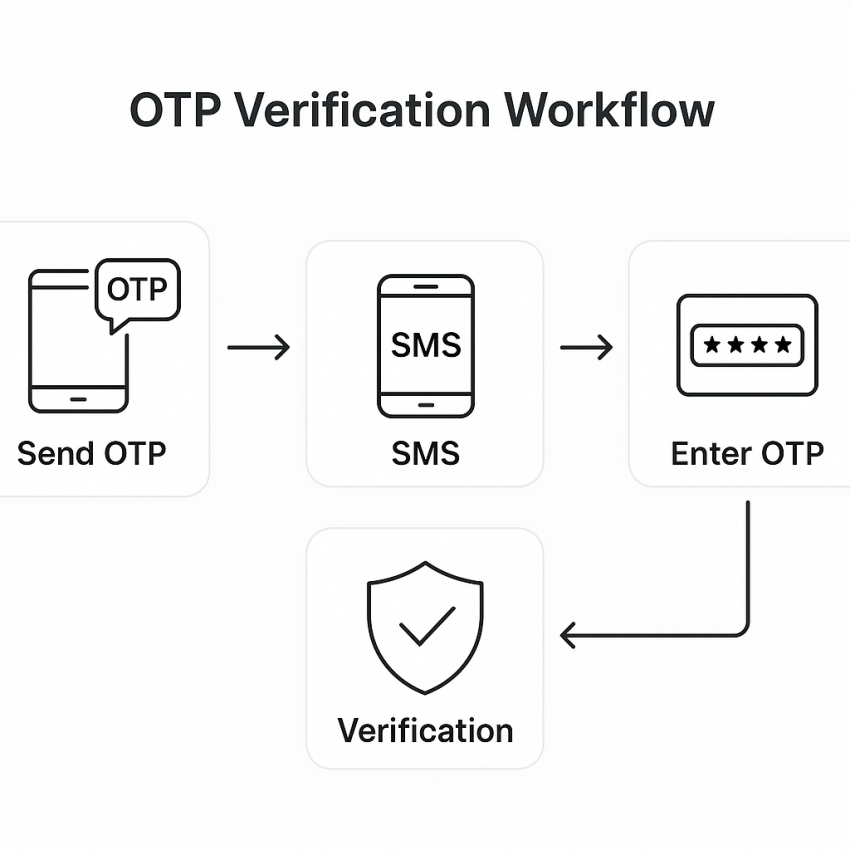
- How does OTP verification work?
- A server generates a code, sends it via a chosen channel (SMS, voice, or app), and validates the entered code within a short window.
- Is OTP verification secure?
- It adds a dynamic barrier, but its security depends on delivery channel, code length, and rate limiting.
- What delivery method should I choose?
- Assess your audience, risk level, and device availability; consider app-based or push-based tokens for higher security.
- How can I troubleshoot OTP delivery problems?
- Check network coverage, ensure codes are not cached, and monitor throttling; verify time synchronization for TOTP-based schemes.
- Can I use OTP for all services?
- Yes, but tailor delivery methods to service sensitivity and user experience; always provide a fallback option.